Cyber Security Course in Hyderabad with 100% Placement Assistance
![]() 4.6 Rating | 1790+ Enrolments | Classroom & Online | Certificate of Completion
4.6 Rating | 1790+ Enrolments | Classroom & Online | Certificate of Completion
Digital Nest offers a cyber security course in Hyderabad. Cybersecurity content is curated by real time experts. Digital Nest is located in Madhapur which is close to the IT Hub of Hyderabad India.
We have a dedicated team for placements, who will assist you in getting placed in top notch companies in Hyderabad who are currently hiring cyber security professionals. Cyber security training in Hyderabad consists of penetration testing and ethical hacking.
We are one of the best institutes in Hyderabad for cybersecurity and ethical hacking. Our institute teaching methodology includes not just theoretical but practical live hands-on training will be provided to the students who opt for cyber security and ethical hacking certification courses.
Enquire : 808-899-8664
2,4 Months
Duration
1000+
Course Enrollments
100%
Placement Assistance
0% EMI
3 Partner Banks
Key Highlights Of Cyber Security Training In Hyderabad
![]() 60+ Learning Hours
60+ Learning Hours
![]() 5 Projects
5 Projects
![]() 15+ Assignments
15+ Assignments
![]() 100% Placements Assistance
100% Placements Assistance
Cyber Security & Ethical Hacking Course Curriculum
Penetration Testing
Vulnerability Assessment & Penetration Testing
• Introduction to the web application Vulnerability Assessment & Penetration Testing
Standards to follow
- OWASP Top 10 Overview
- OWASP Security Testing Methodology
- SANS Top 25 Overview
Intro to Big Bunty Program
- Different Bug Bounty Platforms
- Understanding In-Scope & Out-of-Scope
- Understanding the Vulnerability Priority 4. Explanation about any one Bug bounty platform
- About CTF in bug bounty (i.e. Hackerone)
Application Analysis
- Understanding difference between Static & Dynamic Applications
- Analysis of the application flow
- Different categories of applications
- Analysis of the application functionalities and their functional cycle
Authentication Testing
- About Authentication Process Cycle
- Understanding different login patterns
- Introduction to Burp Suite
- Authentication Bypass using SQL payloads
- Login Brute force
- User Enumeration
- Hard Coded Credentials
- Insecure Logout Implementation
- Strict Transport Security Not Enforced
- Testing OTP Length, Duration & Rate Limitation
- Mobile/Email OTP Bombing
- Leakage of OTP in Later Response
- Response Tampering OTP Bypass
- Testing IDOR – Token Based Authentication
- Sending User Credentials using GET method
Testing the User Registration Process
- About User Registration Process Cycle
- Testing Input Validation – XSS
- Verification of Email address / Mobile Number
- Weak Username or un-enforced policies
- Weak password policies
Testing Password Reset Functionality
- About Password Reset Functionality Cycle
- Testing authorization issue in-case of UID & Token
- Testing Life time of reset link
- Predictability of the token encryption (Base64 based encryption)
- Testing password reset token expiration
Sensitive Data Exposure
- About Sensitive Data Exposure depending on Application Category
- Insecure Error Handling
- Information disclosure via metadata
- Insecure communication channel
- Hidden/sensitive directories & files in robots.txt
- Return of sensitive information in later responses (example: password, otp, other user’s private/sensitive information)
API Communication
- About API Communication
- Authorization Header Analysis
• Basic Authentication token
• Barer Token
• None
• Custom - About JWT Token pattern
- Un-Authenticated/Anonymous Access
Testing for Cookie Attacks
- Understanding the cookie Life Cycle
- Weakness in cookie life cycle
- Cookie with sensitive data
- XSS via cookie
- Missing HTTP only Flag
- Missing Secure Flag
- Analysing authorization/privileges implementation through cookies
Headers and Policy Scrunity
- CRLF Injection
- Host Header Injection
- Cross Origin Resource Sharing
- Click Jacking
- URL Redirection
Session Management Issues
- Testing for Insecure Logout Implementation
- Testing for CSRF Vulnerability
- Bypass Methods of CSRF Vulnerability
Testing for Authorized Testing
- Concept of Access Control & RBAC
- Insecure Direct Object Reference (IDOR)
- Testing for Vertical Privilege Escalation
- Testing Horizontal Privilege Escalation
- Directory Traversal
Data Validation Testing
- Malicious file upload
- Cross Site Scripting
- CSV Injection
- HTTP Parameter Solution
Injections
- Remote Code Execution
- SQL Injection
- XML Injection / XXE
- OS Command Injection
Testing Server Side Issues
- Testing for SSRF
- Template Injection
Business Logic Issues
- About different payment methods Integration
- About Payment Tampering Method
- Straight Forward Payment Tampering
- Add-on Based Payment Tampering
- Coupon Based Payment Tampering
- Longitude and Latitude based payment tampering (In Case of CAB booking, if validation process depends on Long & Lat)
- Failure to Success Journey
- HTTP Parameter pollution (In case of Amount parameter)
- Getting High Benefits Features with Low
- Benefit cost (In case of Feature id)
- Test with Fake DC/CC with CVV
- Sensitive information Leakage
- Insecure Direct Object Reference (Getting Booking & Billing Details, in case of E-Comers application)
- Testing IDOR (In case QR Code generated based on ID value)
- Bypassing Attaching Mandatory Entities
Cloud Misconfiguration
- AWS S3 Misconfiguration
Testing for Security Misconfiguration
- Outdated Framework /CRM/ WordPress
- Enabled Directory Listing
- Default accounts with default passwords
Miscellaneous
- Reflected File Download
- Accessing Default Files (i.e: phpmyadmin)
Other Vulnerabilities
- Web Cache Posioning
Foot Printing & Information Gathering
- About Red Team Assessment overview (RTA)
- Foot Printing & Info Gathering Concepts
API Testing
- Introduction to postman Collection
- Integrating burp proxy to the postman collection.
Ethical Hacking
Introduction to Ethical Hacking:
- Basics of Ethical Hacking
- Types of Hackers
Reconnaissance:
- Information Gathering
- Foot Printing
Kali Linux Basics:
- Basic Commands of Kali Linux
- Configuration of Kali Linux
Password Cracking:
- Password Guessing
- Default passwords
- Password Dictionary Creation
Brute Force Attacks:
- OTP Brute Forcing
- Password Brute Forcing
- Login Brute Forcing
Injection Attacks:
- CSV Injection
- SQL Injection
- XXS Injection
Phishing Attacks:
- Account Handover
Privelege Escalation:
- High Privelege and Low Privelege Escalation
Cryptography:
- Encryption
- Decryption
- Web Application Hacking Basics:
- Mobile Application Hacking:
- Vulnerability Analysis:
- Vulnerability Scanning:
- OWASP Top 10:
- Proxies & VPN:
- HTTP parameter pollution Attack:
- User & Password Enumerations:
Cyber Security & Ethical Hacking Course Description
Enhance your skills in Cyber Security and Ethical Hacking at Digital Nest in Hyderabad. Our comprehensive course offers expert training in the field of Cyber Security and Ethical Hacking with experienced trainers who are industry experts, you’ll receive high quality education.
Digital Nest in Hyderabad, Offers an intensive two-month Cyber Security and Ethical Hacking course that covers essential topics such as Network Security, Web Application Security, Cryptography, Penetration testing and more..
Our hands-on approach allows you to apply your knowledge in real-world scenarios, gaining valuable insights into the latest hacking techniques and defenses. We provide 100% placement assistance by leveraging our industry connections to help you secure rewarding job opportunities.
Our flexible course duration accommodates your schedule while ensuring the comprehensive subject matter is covered.
Our course stands out from other institutes in Hyderabad with its unbeatable affordability, as our fees range from 25,000/- to 40,000/- INR, making it the most cost-effective option for learning Cyber Security and Ethical Hacking skills, making quality education accessible to everyone.
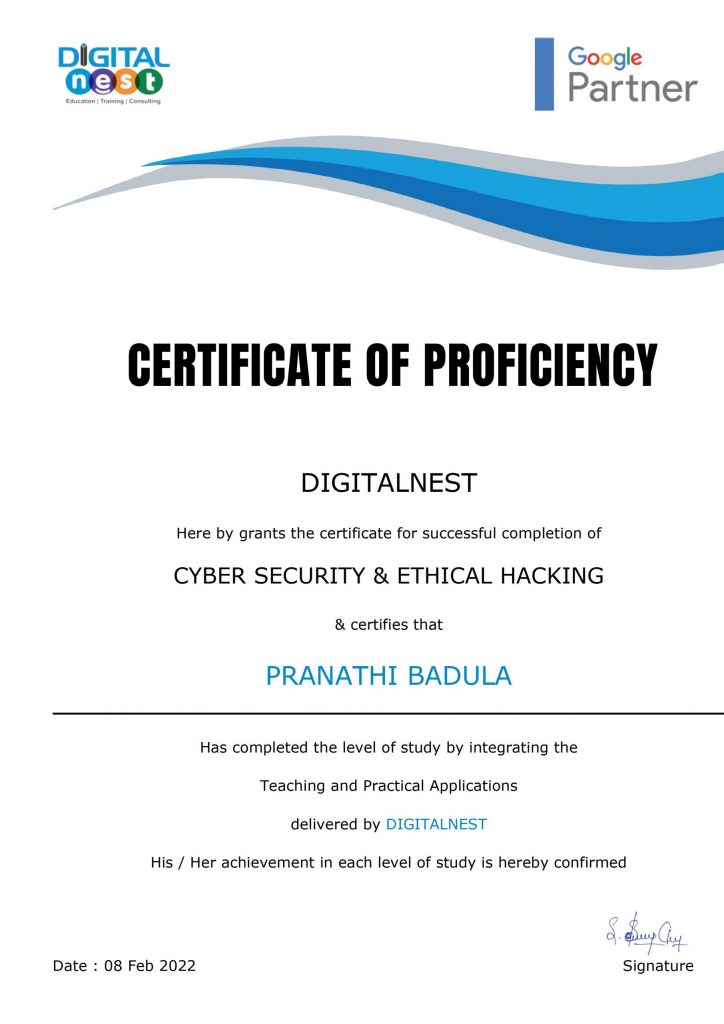
Upon completion you’ll receive an industry-recognized certification, giving you a competitive edge in the job market.
Join digital nest in Hyderabad to learn Cyber Security and Ethical Hacking from our industry experts, Gain practical experience and access our 100% placement assistance. Contact us to gain a spot in our next batch!
At Digital Nest, we understand the dynamic job market demands, which is why we offer a diverse range of courses to cater to various career paths. Our curriculum includes in-demand courses like Digital Marketing and Graphic Designing, both of which boast a strong job market. Explore our Digital Marketing course and Graphic Designing course to acquire valuable skills that can propel your career to new heights.
We have Physical instructor led classes happening at Panjagutta and Hitech City Branches , Hyderabad
We teach Courses online Using tools like zoom, Microsoft Teams
How E-Learning Works?
We have recorded videos of the trainer . This videos were recorded while taking the class. We kept in mind that student should feel the classroom environment while training. we request you to take a trail session. if you are satisfied you can take up the course.
For trail session and more information you can contact digital nest sales team on +91-8088998664 or write us at info@digitalnest.in
We offer special Training for Companies we first understand the company, its services and we will diagnose the present marketing practices and then we prepare a customized curriculum that suits to the needs of that particular company.
For Corporate training you can Reach our Sales Team at +91-8088998664 or you can also write to us at info@digitalnest.in
FAQ’s Of Cyber Security Training
-
What is Cyber Security?
Computer security, cybersecurity, or information technology security is the protection of computer systems and networks from information disclosure, theft of, or damage to their hardware, software, or electronic data, as well as from the disruption or misdirection of the services they provide.
-
Who Can Opt for Cyber Security training?
Any graduate or postgraduate having analytical and logical skills would be the right candidate for the training. B.tech/BE/BBA/MBA/MSc Comp/ Stats/Maths/BSC Comp/Maths/PGDM People who are working in software or decision-making environment can also opt for this course.
-
Do you provide materials and assignments for Cyber Security training?
Yes! We provide module-based material handouts of the data science course that is taught in the class. We also give practical assignments and assessment tests to monitor the student’s progress during the course.
-
How are we different from other institutes?
We are identified as the “Best Training Institute in Hyderabad.” by Times of India in the category of “times education icons.” We conduct Mock Interview Sessions and various types of data science training assignments to face real-time challenges in an effortless manner. We always strive hard to make every Cyber Security trainee Happy, happiness comes when you give first the best industry curriculum, second the best trainers, third the best hands-on training, 4th the best start of art training facility where students can think beyond the box.
-
How is the demand for a Cyber Security course?
Demand for hackers In India companies like wipro, infosys and IBM are interested in employing ethical hackers. Moreover salaries are higher than other areas of IT. According to Nasscom, India will require at least 77,000 ethical hackers compared to the present figure of 15,000.
-
Do you provide placements for Cyber Security training?
Yes! We provide Assured Placement Assistance for our Cyber Security Certification course. We have a dedicated Placement officer at Digital Nest, who’s job is to make sure that students are getting placements alerts and we also invite companies to our academy to hire our Cyber Security trainees.
-
What is the duration of the Cyber Security Course?
Typically the duration of Cyber Security training would last for 2 months. We have designed a curriculum that is very comprehensive in Hyderabad.
-
Where are we located?
Digital Nest has one of the top state of the art training centers in the prime locations in Hyderabad at Panjagutta which is 1 km away from Ameerpet and also one at Hitech City in the Silicon Valley area of Hyderabad.
Get Cyber Security Course Completion Certificate
Become a Certified Ethical Hacker and learn one of employer’s most requested skills of 2023
Course Curriculum has been produced keeping in mind current industry standards and constantly prone to alterations with the latest progressions in the subject
Our
Alumni Testimonials
Rated Avg 4.5* Out Of 5 by 2000+ Learners



Previously i don’t have any knowledge in Cyber Security & Ethical Hacking course.
I searched for the Best Cyber Security training in Hyderabad. Then I found Digital Nest, This is the Best Institute & they taught me from scratch. They also offered me Cyber Security Course Completion certificate and Placement Assistance and today I got placed as Security Engineer
Wanted to take up Cyber Security & Ethical Hacking Courses and checked multiple platforms like UpGrad, Simplilearn. Was very Expensive. Glad that I found Digital Nest offering similar course at best price. Checked their syllabus & found it on par with other big names and joined. In retrospect, one of the best decisions I took. The trainers are friendly & approachable for any doubts, help. The timings are flexible and you can choose to opt online or offline at anytime.
Attended Digital Nest’s Cyber Security Program. The trainer was well experienced & knowledgable. I went to various other institutions and I found that no institute is having the content that Digital Nest is Offering. Then immediately without any second thought I joined Digital Nest. The program co-ordinators are always there if you want to reach out for any help.
I have joined Cyber Security & Ethical Hacking course for 60 days! It was very good interactive program by Digital Nest in Hitech city branch. Trainer is a real time professional and explained concepts with real time scenarios. The most interesting part during the course was dealing with the projects, it was very challenging and thrilling.
Our Cyber Security Students Hail From
Students , Working Professionals & Business Owners From Various Start Ups And MNC’s


